Key Takeaways
- ZK proofs enhance privacy and security but require optimization to scale effectively.
- Scalability challenges include high computation costs, complex data handling, and blockchain integration issues.
- Solutions such as recursive proofs, Layer 2 scaling, optimized cryptographic techniques, and parallel computation help improve scalability.
- Scalable ZK solutions will be crucial for enabling efficient and secure blockchain applications in the future.
Understanding Scalability in ZK Proofs
Scalability in blockchain refers to the system’s ability to handle increasing transaction loads without compromising speed or security. ZK proofs, while valuable for enhancing privacy and security, often require significant computational resources. To be practical for large-scale applications, ZK proof systems must optimize their performance in three key areas:
- Proof Generation Time – Reducing the time it takes to generate a proof.
- Verification Time – Ensuring that proofs can be quickly verified by validators.
- Storage Efficiency – Keeping proof sizes manageable for on-chain storage.
Challenges of Scaling ZK Proofs
Despite their benefits, ZK proofs present several scalability challenges:
- High Computation Costs – Generating and verifying proofs can be resource-intensive.
- Data Complexity – Handling large datasets increases the complexity of proof generation.
- Blockchain Integration – Ensuring ZK proofs work efficiently within blockchain architectures without increasing transaction times or costs.
Solutions for Enhancing ZK Scalability
To address these challenges, developers and researchers have introduced various approaches:
1. Recursive Proofs
Recursive ZK proofs allow multiple proofs to be combined into a single, smaller proof. This reduces the computational burden and makes verification faster, enabling blockchains to process more transactions efficiently.
2. Layer 2 Scaling Solutions
Layer 2 solutions, such as rollups, leverage ZK proofs to batch transactions off-chain before submitting a single proof to the main blockchain. This significantly reduces network congestion and transaction costs.
3. Optimized Cryptographic Techniques
New cryptographic protocols, such as STARKs (Scalable Transparent Argument of Knowledge), provide a more efficient way to generate and verify ZK proofs without relying on a trusted setup, making them more scalable and decentralized.
4. Parallel Computation
By utilizing parallel processing, proof generation can be distributed across multiple processors, significantly reducing the time required to generate complex proofs.
The Road Ahead
Scalable ZK solutions are transforming blockchain technology, making it more efficient, secure, and capable of handling complex transactions. By reducing computational bottlenecks and optimizing verification processes, ZK proofs pave the way for greater adoption of decentralized applications. As research and development continue, the future of blockchain scalability will rely heavily on advanced cryptographic techniques and innovative scaling solutions.
The future of blockchain isn’t just about decentralization—it’s about efficiency, accessibility, and security for all users.
FAQ
Q: What are Zero-Knowledge (ZK) proofs? A: ZK proofs are cryptographic methods that allow one party to prove knowledge of a statement without revealing the actual data.
Q: Why is scalability important for ZK proofs? A: As blockchain applications grow, ZK proofs must be optimized to handle larger datasets and complex computations efficiently.
Q: How do recursive ZK proofs improve scalability? A: Recursive proofs allow multiple proofs to be combined into one, reducing computation time and improving verification efficiency.
Q: What role do Layer 2 solutions play in ZK scalability? A: Layer 2 solutions use ZK proofs to batch multiple transactions off-chain, reducing congestion and lowering costs on the main blockchain.
Q: What are the benefits of STARKs over other ZK proofs? A: STARKs offer greater scalability and security without requiring a trusted setup, making them more efficient for large-scale applications.
 Stay Ahead in Blockchain & Cryptography
Stay Ahead in Blockchain & Cryptography
Zero-Knowledge proofs and scalability solutions are shaping the next generation of blockchain technology. Stay informed on the latest advancements in decentralized security by following Ontology’s latest updates.
 Further Reading – Explore More on ZK Scalability
Further Reading – Explore More on ZK Scalability
By leveraging scalable ZK solutions, blockchain networks can improve performance, enhance privacy, and support more complex applications, paving the way for broader adoption in the Web3 ecosystem.
In recent years, the world of memes has evolved from amusing internet content into a lucrative business, especially in places like Thailand. Thai influencers are turning memes into money-making opportunities by tapping into popular culture and creative marketing strategies. With the right approach, these influencers are proving that memes can be much more than just a source of entertainment; they can also be a significant income stream.
The rise of meme culture is particularly noticeable in Thailand, where influencers are using their unique styles to engage audiences effectively. By integrating humor with marketing, these influencers attract a large following, which makes them appealing to brands. This ability to draw attention has opened doors to numerous monetization avenues, such as selling shoutouts or collaborating with brands for promotions.
Understanding how Thai influencers succeed in monetizing their meme content offers valuable lessons. Their success stories shed light on methods for growing audiences and employing innovative tactics for financial gain. Through careful analysis of metrics and audience feedback, these influencers continue to refine their strategies to stay ahead in the ever-evolving world of social media.
Key Takeaways
- Memes are a lucrative opportunity for Thai influencers.
- Successful monetization involves engaging content and audience growth.
- Future success depends on adapting and innovating strategies.
The Rise of Meme Culture in Thailand
Meme culture in Thailand has become a significant force, especially in the realms of digital entertainment and marketing. The increasing use of social media platforms has fueled this growth, making memes an integral part of online communication and brand engagement.
Historical Context of Memes
Memes started gaining traction in Thailand with the widespread availability of the internet and smartphones, which enabled easy access to global social media. Initially, memes circulated within niche online communities, centered around humor and local cultural references.
As digital platforms like Facebook and Twitter grew, so did the diversity of memes. They began to reflect not just humor but also social and political commentary. Thai netizens used memes to share viewpoints on current events, often offering a humorous twist to serious topics. Over time, popular memes became a cultural staple, widely shared among users.
Thai influencers took notice of this trend, leveraging the viral nature of memes to grow their audiences. Memes became a tool for storytelling, merging entertainment with engagement, important for digital content creators.
Significance of Memes in Thai Digital Ecosystem
In Thailand’s digital landscape, memes serve as a bridge connecting brands with younger audiences. Influencers use them to craft relatable content, making brands more appealing and approachable. This is crucial in a market where traditional advertising might not resonate strongly with digital-savvy users.
Thai influencers adeptly use memes to monetize their online presence. They incorporate local nuances that resonate with audiences, creating a unique blend of humor, culture, and personal stories. This strategy has proven effective in driving brand engagement and awareness. Many brands now see memes as a key part of their digital marketing efforts, frequently employing them in campaigns.
The growing influence of memes in online commerce and advertising in Thailand showcases their importance in shaping digital trends.
Foundations of Monetization
Monetizing memes involves understanding their inherent value, choosing the right platforms for sharing, and navigating the legal aspects. Here’s how creators can effectively use these foundations to earn from their meme content.
Understanding Meme Value
Memes gain value from their ability to engage and resonate with audiences. They often reflect cultural trends or popular topics, making them relatable. Successful memes use humor or emotion to capture attention quickly. A meme’s potential to go viral enhances its value, as it reaches a wider audience, thus increasing potential earnings.
Creators should assess the relevance and timeliness of their content. They should also consider the elements that make a meme shareable, such as humor, clarity, and visual appeal. Monitoring trends and audience responses can inform which memes might achieve higher engagement and, by extension, monetization potential.
Platforms for Monetization
Different platforms offer varying opportunities for meme monetization. Facebook, for instance, allows for ad placements on popular pages, and influencers can earn through platforms like Patreon or Ko-fi. On Instagram, brand collaborations can be beneficial. YouTube channels featuring meme compilations can monetize through ads.
For large Facebook pages, strategies include using brand promotion to generate income. Brands pay influencers to promote their products, providing a steady income stream. Navigating each platform’s specific rules and functionality is crucial for maximizing earnings and maintaining monetization features.
Legal Considerations
Legal issues can arise when monetizing memes, especially regarding copyright. Memes that use copyrighted material without permission may lead to legal consequences. Understanding the limits of fair use is important for creators to avoid potential infringement. Creators should also be aware of platform policies regarding content use and monetization.
Sometimes, memes involve user-generated content or trademarks. In such cases, obtaining necessary permissions or licenses can prevent legal challenges. Additionally, social media platforms have rules that govern content monetization. Adherence to these policies ensures sustained revenue and access to monetization tools.
Case Studies: Thai Influencers’ Success Stories
Thai influencers have made significant strides in monetizing digital content, employing diverse strategies to boost their financial returns. By examining their approaches, one can learn how to successfully engage audiences and diversify income streams.
In-Depth Analysis of Successful Strategies
Many Thai influencers have thrived by leveraging personal stories to create authentic connections with their audience. Using platforms like Pantip.com and Dek-D.com, they share relatable content such as beauty advice and lifestyle tips. This personal approach not only builds trust but also encourages audience engagement.
For example, some influencers focus on niche markets, catering specifically to fans of certain beauty trends. By understanding their audience’s preferences, these influencers tailor content that feels customized and relevant. Their success often stems from consistently delivering high-quality, engaging posts that resonate with followers, leading to increased brand partnerships and collaborations.
Diversification of Revenue Streams
In addition to sponsored posts and collaborations, Thai influencers often explore a variety of monetization methods. By learning from trends, such as those highlighted in discussions about beauty culture, they can effectively broaden their revenue base.
Products like merchandise or exclusive content subscriptions are popular ways to solidify earnings. Some influencers also generate income through live-streaming services where they interact with fans in real-time, adding another dynamic dimension to their brand.
By adopting multiple revenue streams, influencers can minimize risk and increase financial stability. Through these strategies, they create a sustainable business model that capitalizes on their creativity and audience reach.
Engagement Tactics and Audience Growth
Thai influencers employ clever techniques to keep their audiences engaged while also expanding their reach. Key strategies include creating content that resonates with followers and building a loyal community.
Content that Resonates with Audiences
For Thai influencers, creating content that strikes a chord with their audience is essential. Memes often serve as a powerful tool in this regard. They are humorous, relatable, and can spread quickly across social platforms. This makes them ideal for enhancing brand visibility and engagement.
Using culturally relevant humor and trending topics helps capture attention. Successful influencers often stay updated with the latest trends, ensuring their content feels timely and fresh. Collaborations with other influencers can also introduce their content to new audiences.
Thorough audience analysis is vital. It helps in crafting messages that not only entertain but also align with audience values and interests. Thai influencers often tailor their memes to suit the preferences of different demographic groups.
Building and Maintaining a Following
Consistency is key in building a loyal following. Regular posting schedules keep audiences engaged and looking forward to new content. Thai influencers often maintain a balance between promotional and personal posts to avoid overwhelming their audience with advertisements.
Interactive content, like polls or Q&A sessions, encourages audience participation. This helps build a sense of community and connection. Engaging directly with followers through comments or messages demonstrates authenticity and accessibility.
Using Instagram as a primary platform provides influencers with various tools to connect effectively. Features like Instagram Stories allow influencers to share snippets of their daily lives, reinforcing a more personal connection with their followers.
Innovative Monetization Strategies
Thai influencers have developed several innovative ways to monetize their content. By leveraging brand partnerships, exploring merchandising opportunities, and utilizing digital goods, they have created revenue streams that go beyond traditional methods. These strategies are not only inventive but also highly effective in engaging audiences.
Brand Partnerships and Sponsorships
Many Thai influencers use brand partnerships and sponsorships to earn revenue. By collaborating with companies that align with their personal brand, they can provide authentic endorsements that resonate with their followers. Influencers often create engaging content that showcases products in real-life scenarios, making the promotion genuine and relatable.
These partnerships can include sponsored posts, product placements, or social media takeovers. Influencers may receive compensation in the form of payments, free products, or both. Selecting brands that match their values is crucial for building trust with their audience. This approach not only benefits the influencer but also helps brands reach a wider, more targeted audience.
Merchandising and Licensing Opportunities
Influencers can capitalize on their popularity by launching merchandise and licensing their image or brand. This can include selling products like clothes, accessories, or even custom-made items unique to their personal brand. By doing so, they offer fans a tangible way to connect with their favorite online personalities.
Merchandising requires a good understanding of what the audience values. Successful influencers often create exclusive or limited-edition items to enhance appeal. Additionally, licensing deals can open doors to new arenas such as toys or games, broadening the scope of their brand. This strategy allows influencers to diversify their income while strengthening their market presence.
Digital and Virtual Goods
In the digital age, offering virtual goods is a cutting-edge monetization strategy. Thai influencers have embraced digital products like e-books, online courses, or membership programs. These goods can tap into the growing demand for exclusive content and community engagement.
Virtual goods allow for flexible pricing and a broad audience reach, offering fans unique experiences without physical delivery. By creating high-value digital materials or exclusive online communities, influencers build loyalty and generate recurring income. The ability to instantly deliver content also makes this approach efficient and scalable, further enhancing an influencer’s earning potential.
Metrics and Analytics for Meme Monetization
Monetizing memes effectively requires understanding which metrics indicate success and how to adapt campaigns to align with audience trends. Successful meme strategies rely on calculating return on investment (ROI) and adjusting according to audience preferences.
Tracking Success and ROI
Tracking the success of meme campaigns involves examining various key performance indicators (KPIs). These include engagement metrics such as likes, shares, and comments, which reveal how well the meme resonates with the audience. It’s also essential to measure reach and impressions to determine how widely the meme is being viewed.
For monetization, conversion rates are crucial. These metrics show how many viewers take action from seeing the meme, such as visiting a website or making a purchase. Analyzing meme campaigns involves comparing the cost of creating and promoting memes against generated revenue. Effective strategies often utilize tools like Google Analytics and social media insights to obtain precise data on audience interaction.
Adapting to Trends and Audience Preferences
Adapting to changing trends and audience preferences ensures meme campaigns remain relevant and effective. This means constantly monitoring social media platforms to spot emerging trends. Popular hashtags, viral topics, and seasonal content often indicate shifts in audience interest.
Thai influencers often excel at this by crafting memes that resonate with their audience’s current mood and cultural context. By studying reactions and feedback to previous content, creators can improve future meme success. Audience demographics and preferences should be regularly analyzed using social media analytics tools. Understanding these elements allows influencers to fine-tune their content for maximum engagement and impact, securing better monetization opportunities.
Challenges and Considerations
Monetizing memes involves various challenges. Thai influencers and brands must balance engaging content with the risk of oversaturation, while also considering ethical questions about brand partnerships and audience reactions.
Navigating Virality and Saturation
Thai influencers often rely on the viral nature of memes to boost their brand visibility. Yet, achieving viral success is unpredictable since it depends on timing, audience engagement, and an element of luck. Overuse of memes can lead to content saturation, making it harder for new memes to capture attention. Brands and influencers must continuously innovate and adapt to maintain relevance and interest. Strategies may include collaborating with other creators or tapping into trending topics to keep the content fresh and exciting.
Ethical Implications and Public Perception
Monetizing memes raises ethical concerns for Thai influencers. They often collaborate with brands, walking a fine line between authentic content and sponsored promotions. This can affect how audiences perceive them. If fans feel content is too promotional or not genuine, influencers risk losing trust and followers. Transparency becomes crucial in maintaining credibility. Furthermore, cultural sensitivity is important, as memes can sometimes unintentionally offend certain groups. Influencers are advised to remain aware of these considerations to align with audience values and maintain a positive public image.
Future Outlook on Meme Monetization
The future of meme monetization involves exploring new trends and developing strategies for influencers. As digital culture evolves, meme enthusiasts and content creators need to adapt to stay relevant and profitable.
Predicting Trends and Innovations
The role of influencers in meme culture is expanding. With platforms like TikTok and Instagram, influencers can boost meme visibility rapidly. Virtual reality and augmented reality are emerging technologies that could enhance how users experience memes, creating new opportunities for interactive content.
Meme coins are a growing phenomenon, with some predicting they will change the landscape of digital currency. The support of meme coins by popular influencers is opening ways to manage tokens through social power. Strategies like token giveaways and rewards can engage communities and encourage participation.
Video content is becoming more important. Influencers creating videos about meme trends or “how to” guides can capitalize on the growing audience interested in this medium. This approach not only drives engagement but also opens up potential revenue streams from ad partnerships.
Long-Term Strategies for Influencers
Influencers must build authentic connections with their audience. Engaging with followers through Q&A sessions or live streams keeps the community active and invested. This connection fosters loyalty and trust, essential for long-term success.
Diversifying content is key for longevity. Influencers should branch out beyond memes to related content areas such as pop culture commentary or news. This strategy can attract a broader audience, which is beneficial for sustainable growth.
Leveraging analytics tools to track engagement metrics allows influencers to understand what content resonates most with their audience. By focusing on high-impact content, they can refine their efforts to capture and maintain audience interest over time.
Frequently Asked Questions
Monetizing memes involves various strategies and considerations. Thai influencers have effectively harnessed meme culture to generate income on platforms like Instagram and TikTok, while navigating legal factors and measuring success.
What are successful strategies for making money from memes on social media platforms?
Successful strategies include affiliate marketing, brand partnerships, and selling merchandise. Influencers can join affiliate programs or partner with brands to receive payment for promoting products. Selling meme-themed merchandise, such as T-shirts or mugs, is another way to generate income from viral content.
How have Thai influencers capitalized on meme culture to generate income?
Thai influencers have tapped into meme culture by creating relatable and culturally relevant content. They often collaborate with brands to incorporate memes into marketing campaigns, increasing engagement and attracting sponsorships. Some influencers manage to leverage their large followings to drive traffic to other monetized channels like blogs or online stores.
What are the key factors to consider when turning viral content into a source of revenue?
Key factors include understanding target audiences and maintaining content authenticity. Influencers must also keep up with trends and create original content that resonates with followers. It’s crucial to balance monetization efforts with the free nature of meme sharing to avoid alienating audiences.
Can posting memes on platforms like YouTube, TikTok, and Instagram lead to significant earnings?
Yes, posting memes on these platforms can lead to significant earnings through ad revenue, sponsorships, and merchandise sales. Creators with a large audience can attract brands looking for advertising opportunities. Each platform has its own monetization features, allowing creators to earn revenue based on views and engagement.
What are the legal considerations when using popular memes for monetization purposes?
Legal considerations include copyright issues and fair use policies. Creators must ensure they have permission to use certain images or characters in their content. It’s important to avoid infringing on intellectual property rights, which could lead to legal disputes or loss of revenue opportunities.
How does one measure the financial success of meme-centered marketing campaigns?
Measuring the success of meme-centered campaigns involves tracking metrics like engagement rates, follower growth, and revenue increases. Analytics tools can provide insights into how well the content performed. Additionally, conversion rates for any promoted products or services can indicate the effectiveness of monetization strategies.
]]>Crypto can be a daunting world for newcomers, filled with a lot of technical jargon and complex concepts. Memes can help to break down these barriers, making crypto more accessible and understandable for new users. Memes use humor and relatable scenarios to explain what might otherwise be overwhelming financial and technical ideas.
In the crypto community, memes serve as a unique tool, especially for beginners. By presenting information in a fun and digestible way, they help bridge the gap between intricate concepts and everyday understanding. This approach encourages more people to explore cryptocurrencies without feeling intimidated.
Memes also contribute to building a sense of community among crypto enthusiasts. They have a shared culture and collective learning experience that draws people in. This community aspect is crucial for boosting engagement and promoting the adoption of digital currencies.
Key Takeaways
- Memes simplify complex crypto concepts.
- They foster community among crypto users.
- They encourage crypto adoption by making it approachable.
The Role of Memes in Crypto Education
Memes have become a powerful tool in the crypto world, making complex ideas easier to understand. They help people learn visually and spark conversations about cryptocurrencies.
Visual Learning Through Memes
Memes often use visuals to explain crypto concepts. By turning complicated ideas into eye-catching images, they make information easier to remember. Newcomers can quickly grasp how blockchain works or what a meme coin is. Visuals cut through the clutter and offer bite-sized learning without jargon. Memes use humor and relatable scenarios to break down barriers, making topics like trading or investing less intimidating for beginners.
The rise of Meme Coin Development shows the importance of visuals. Memes make use of familiar formats like cartoon characters or famous quotes to teach about risks and benefits. This approach turns learning into an engaging experience, increasing retention and understanding.
Memes as Conversation Starters
Memes are also great for starting discussions. They encourage dialogue by presenting crypto information in a fun and accessible manner. Individuals share memes to highlight trends or issues, fostering a sense of community. Sharing and discussing these memes on social media platforms gets more people interested in cryptocurrencies.
For example, memes have impacted the growth of meme coins. These informal, humorous sketches open up conversations about investing and finance. Discussing the insights shared through memes helps people feel more connected and informed. Memes not only educate but also build bridges among diverse individuals curious about the crypto world.
Memes and Community Building
Memes have a unique ability to bring people together in the crypto world. They create shared experiences and foster inclusivity among both enthusiasts and newcomers by using humor and cultural references that are easily understood.
Creating Shared Experiences
Memes often serve as a bridge connecting diverse individuals with a common interest in cryptocurrency. By using humor and relevant cultural references, memes make complex topics more accessible. They break down barriers and allow people to engage without feeling overwhelmed. This process of shared understanding helps build a stronger sense of community.
Through platforms like social media, users share memes widely, sparking conversations and inside jokes among crypto enthusiasts. This shared culture strengthens group identity, making newcomers feel welcome. As participation grows, the community becomes more cohesive, facilitating quicker knowledge exchange.
Fostering Inclusivity Among Newcomers
Memes act as an entry point for those new to cryptocurrency. Their humor and simplicity make complicated concepts easier to grasp. By simplifying complex ideas, memes help demystify the crypto space, making it less intimidating. This approach encourages more people to participate and learn at their own pace.
In addition, the use of memes often signals that a community is open to diverse voices. This sense of inclusivity builds trust among newcomers. As they engage more with meme-based content, they become part of ongoing conversations, slowly integrating into the community.
Overall, memes help create an inviting environment where everyone can learn, share, and grow together in the world of cryptocurrency.
Translating Complex Concepts
Memes transform intricate crypto topics into easy-to-understand visuals and text. By using humor and relatable imagery, they help break down tough jargon and highlight emerging trends.
Simplifying Technical Jargon
Cryptocurrency comes with its own set of technical terms that can be confusing for newcomers. Memes are effective tools to break down this jargon into simple language. For instance, memes can depict complex ideas like blockchain or decentralized finance in a relatable way.
An image featuring a playful character alongside a brief text can replace lengthy explanations. Visuals help the audience grasp difficult ideas quickly and remember them better. The internet is a rich source of memes that explain confusing terms through simple analogies, making crypto more approachable for everyone.
Highlighting Crypto Trends with Humor
Crypto trends are ever-changing and hard to track. Memes offer a fun way to stay updated. They distill complex news into a laughable moment, making it easier for people to discuss and remember. Humor captures attention and encourages sharing among friends, expanding the reach of essential updates.
For example, trends like NFT booms or Bitcoin price changes can be shared through creative, humorous memes. By transforming detailed data into amusing posts, people can quickly comprehend what’s happening in the crypto world. Memes act as a bridge, connecting technical aspects with day-to-day conversations about cryptocurrency advancements.
Impact on Cryptocurrency Adoption
Memes have played a crucial role in making cryptocurrency more accessible to new users. They simplify complex concepts and spark curiosity among potential investors, helping to increase participation in the crypto space.
Increasing Accessibility to Crypto Information
Memes have transformed the way people perceive cryptocurrency. By using humor and popular culture references, memes break down technical jargon into digestible bits. This can make it easier for newcomers to understand basic crypto concepts without feeling overwhelmed. For instance, platforms like Binance highlight how memecoins serve as entry points for first-time investors. These coins often feature recognizable meme characters, which attract people unfamiliar with traditional financial systems. As a result, potential investors might feel less intimidated and more curious about diving into the crypto world. Additionally, memes circulate rapidly across social media, reaching audiences who might not actively search for financial information.
Encouraging the Curiosity of New Investors
Memes have a unique way of capturing attention and sparking interest among potential crypto investors. They often use humor to touch on trends or market movements, making the subject engaging and relatable. According to Coinsniper, memes have inspired the creation of meme coins, which themselves become subjects of viral trends. This virality prompts newcomers to ask questions and seek more information about crypto assets. By drawing people in with familiar and amusing content, memes cultivate an environment where learning feels less daunting. New users may be more willing to explore, invest, and participate in discussions, leading to increased adoption and interest in the broader cryptocurrency market.
 Beyond memes, blockchain projects like Ontology are actively working to make crypto more accessible. Read more about recent developments in Web3 on Ontology’s news page.
Beyond memes, blockchain projects like Ontology are actively working to make crypto more accessible. Read more about recent developments in Web3 on Ontology’s news page. 
The Downside of Memes in Crypto
While memes simplify crypto concepts and drive adoption, they also come with drawbacks like misinformation and challenges in responsible sharing. These issues can mislead investors and create confusion for new users. Understanding these downsides is crucial for anyone navigating the crypto space.
Spreading Misinformation
Memes often simplify complex crypto topics, but this can lead to spreading misinformation. Some memes might exaggerate a coin’s potential, promoting a false sense of security. Users might invest based on memes instead of doing thorough research, which can be risky.
Memes can create hype around a coin without fundamental value. This hype-driven investment can cause financial losses when reality sets in. New investors may not realize the speculative nature of meme coins and might allocate significant funds based on hype alone. It is essential to verify information and differentiate between playful content and actual crypto analysis.
Challenges in Ensuring Responsible Sharing
Ensuring responsible sharing of memes is another stumbling block. Some memes can unintentionally encourage harmful behaviors. They may suggest unrealistic investment returns or downplay risks, enticing inexperienced users to jump into potentially unstable projects.
Since memes are easily shared, they gain rapid traction across platforms. This viral spread can lead to narrative control by a few influencers, skewing the public’s perception. To combat this, users need to be educated about discerning credible information and staying skeptical of overly positive or negative representations. More balanced sharing can help maintain a healthy, informed crypto community.
Frequently Asked Questions
Meme coins offer a playful entry point into cryptocurrencies, combining humor with digital finance. Here are some common inquiries to help understand their role and impact.
What is the difference between a meme coin and traditional cryptocurrency?
Meme coins are cryptocurrency variations inspired by internet memes or pop culture, such as Dogecoin. Traditional cryptocurrencies like Bitcoin focus on technological innovation and financial use cases, while meme coins often emphasize community and engagement.
What are some typical uses for meme coins within the cryptocurrency community?
Within the crypto community, meme coins are used for fun exchanges and community-building. They encourage user interaction and often lead to playful social media campaigns. Some even support charitable causes and crowdfunding efforts.
Which meme coin is considered to have the greatest potential for growth?
Dogecoin is often cited for its strong community and widespread recognition, potentially making it a candidate for growth. However, the potential for all meme coins can be unpredictable due to market volatility.
How do meme coins generally gain value in the market?
Meme coins gain value through community interest and social media buzz. Influential endorsements, viral trends, and media coverage often drive their popularity and market price.
Can meme coins be considered a serious investment for the future?
While some investors speculate on meme coins like Dogecoin, their unpredictable nature and community-driven value can make them risky. They are often not considered reliable long-term investments compared to traditional cryptocurrencies.
What are some noteworthy examples of meme coins?
Some popular meme coins include Dogecoin and Shiba Inu. Both have gained notoriety for their playful origins and dedicated online communities.
 Stay Updated on Crypto and Web3 Trends
Stay Updated on Crypto and Web3 Trends
Memes are just one way the crypto space is evolving. Stay informed about the latest developments in blockchain, decentralized identity, and crypto adoption on Ontology News.
 Further Reading
Further Reading
 Get involved with our active community across social!
Get involved with our active community across social!
Cryptography is the backbone of blockchain technology, ensuring the security and integrity of transactions. Blockchain employs various cryptographic techniques like hashing, digital signatures, and public/private key pairs to protect data and verify transactions. These methods make it nearly impossible for unauthorized parties to alter transaction data without detection.
One of the primary cryptographic methods used is hashing, which converts input data into a fixed-length string of characters. This unique output, or hash, is crucial for maintaining the integrity of the blockchain. Digital signatures provide another layer of security by authenticating the identity of users and ensuring that transactions are authorized.
Public and private keys are essential for encrypting and decrypting transaction information. By using these keys, blockchain networks can ensure that only authorized parties can access sensitive data, safeguarding against fraud and unauthorized access. These robust cryptographic techniques are vital for maintaining trust and security in blockchain transactions.
Key Points
- Core Cryptographic Methods: Hashing and digital signatures form the foundation of blockchain security, ensuring data integrity and user authentication. Public/private key pairs enable secure data encryption and decryption.
- Advanced Privacy and Security Techniques: Zero-Knowledge Proofs (ZKPs), like zk-SNARKs and zk-STARKs, allow for transaction verification without revealing private data. Homomorphic Encryption permits calculations on encrypted data, enhancing privacy.
- Transaction Verification and Security Protocols: Consensus algorithms (Proof of Work, Proof of Stake) and Merkle Trees are crucial for validating transactions and maintaining the blockchain’s integrity. Transport Layer Security (TLS) and end-to-end encryption protect data during transmission.
- Smart Contracts and Regulatory Compliance: Security tools like formal verification and static/dynamic analysis ensure smart contracts are secure and operate as intended. AML and KYC policies enforce regulatory compliance, preventing fraud and enhancing trust in blockchain systems.
Fundamentals of Blockchain Security
Blockchain security relies on several key cryptographic techniques to ensure data integrity and secure transactions. The most critical elements include cryptographic hash functions, public key cryptography, and digital signatures.
Cryptographic Hash Functions
Cryptographic hash functions play a pivotal role in blockchain technology. They convert data of any size into a fixed-size hash. This hash is unique to the data input, meaning even a minor change in the input results in a vastly different hash. SHA-256 is a commonly used hash function in many blockchain platforms.
These functions are designed to be one-way — it is computationally infeasible to reverse the process and retrieve the original input from the hash. This characteristic ensures the integrity and immutability of blockchain data. The hash functions also provide consensus mechanisms with efficient data verification capabilities, preventing tampering and ensuring trust within the network.
Public Key Cryptography
Public key cryptography underpins the security and privacy of blockchain transactions. Each participant has a pair of cryptographic keys: a public key and a private key. The public key can be shared openly, while the private key must remain confidential.
Transactions are encrypted with the recipient’s public key and can only be decrypted by their private key. This asymmetrical encryption provides a robust privacy layer, ensuring that only the intended recipient can access the transaction details. It also plays a crucial role in user authentication, as participants can verify ownership without revealing their private keys.
Digital Signatures
Digital signatures ensure the authenticity and integrity of transactions within the blockchain. They work by generating a unique signature using a sender’s private key and the transaction data. This signature is then attached to the transaction and verified by network nodes using the sender’s public key.If the signature is valid, it confirms the transaction’s origin and that it hasn’t been altered. Digital signatures provide non-repudiation, meaning the sender cannot deny having initiated a transaction. This aspect is essential for maintaining trust and accountability within the blockchain ecosystem.
Emerging Cryptographic Techniques
New cryptographic methods are enhancing blockchain security, focusing on privacy, data integrity, and collaboration without trust. These cutting-edge techniques include Zero-Knowledge Proofs, Homomorphic Encryption, and Secure Multi-Party Computation.
Zero-Knowledge ProofsZero-knowledge proofs (ZKPs) allow one party to prove to another that a statement is true without revealing any other information. This technology ensures transaction privacy and confidentiality in blockchain networks.
Popular implementations of ZKPs include zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Arguments of Knowledge) and zk-STARKs (Zero-Knowledge Scalable Transparent Arguments of Knowledge). ZKPs are critical in blockchain use cases like confidential transactions and identity verification, aiming to protect sensitive information while still maintaining network security and trust.
Homomorphic Encryption
Homomorphic encryption (HE) lets computations be carried out on encrypted data without needing to decrypt it first. This is revolutionary for data privacy.In blockchains, HE can be used to process transactions or run smart contracts on encrypted data, ensuring full privacy. Despite its high computational cost, advancements are making it more practical. Implementations such as the BGV scheme (Brakerski-Gentry-Vaikuntanathan) are prominently used. HE holds promise in sectors requiring high confidentiality, like finance and healthcare.
Secure Multi-Party Computation
Secure Multi-Party Computation (MPC) enables multiple parties to collaboratively compute a function over their inputs while keeping those inputs private.In blockchain, MPC facilitates decentralized control and eliminates the need for trusted third parties. Applications include shared control of private keys and collaborative decision-making. MPC protocols, such as Yao’s Garbled Circuits and Shamir’s Secret Sharing, are widely implemented. The decentralized approach bolsters security and trust in blockchain transactions, crucial for scenarios where mutual mistrust exists among participants.
Transaction Verification
Effective verification is crucial in blockchain to ensure that transactions are valid and secure. Essential methods for achieving this include consensus algorithms and Merkle trees.
Consensus Algorithms
Consensus algorithms ensure that all nodes in the network agree on the state of the blockchain. Popular consensus algorithms include Proof of Work (PoW), Proof of Stake (PoS), and Delegated Proof of Stake (DPoS).
- Proof of Work (PoW): Miners solve computationally intensive puzzles to validate transactions and add new blocks.
- Proof of Stake (PoS): Validators are chosen based on the number of coins they hold and are willing to “stake” as collateral.
- Delegated Proof of Stake (DPoS): Stakeholders elect a small number of delegates to approve transactions and create blocks.
Encryption Protocols for Transactions
Encryption protocols play a vital role in securing blockchain transactions. Transport Layer Security (TLS) ensures secure communication between nodes, while end-to-end encryption methods provide robust protection for transaction data.
Transport Layer Security (TLS) for Nodes Communication
Transport Layer Security (TLS) is widely used to secure communications between network nodes. It relies on a complex handshake process to authenticate both parties before establishing an encrypted channel. This ensures that data transmitted between nodes is shielded from eavesdropping or tampering. TLS leverages public key infrastructure (PKI) to exchange encryption keys securely. Additionally, it uses a combination of symmetric and asymmetric encryption to maintain data confidentiality and integrity. The symmetric key, used for the encryption of bulk data, is only shared after a secure agreement using asymmetric encryption.
End-to-End Encryption Methods
End-to-end encryption ensures that transaction data is accessible only to the sender and recipient. Techniques such as Elliptic Curve Cryptography (ECC) and Advanced Encryption Standard (AES) are commonly deployed. ECC is favored for its efficient key generation and strong security with relatively small key sizes.AES, on the other hand, is effective for encrypting transaction data due to its speed and resistance to attacks. The combination of ECC for key agreement and AES for data encapsulation forms a robust end-to-end encryption strategy. This dual approach not only encrypts the transaction data but also keeps it safe during transmission.
Decentralized Identifiers (DIDs)
Decentralized Identifiers (DIDs) represent a new paradigm for digital identity, enhancing privacy and security. These identifiers allow individuals to control their digital presence without relying on a central authority.
Self-Sovereign Identity (SSI)
Self-Sovereign Identity (SSI) empowers individuals to own and manage their identities. With SSI, users can create and control their personal identifiers, enabling secure, peer-to-peer transactions.
DIDs are foundational to SSI, functioning without centralized registries. Each DID is associated with a cryptographic keypair, allowing for secure proof of identity.Furthermore, DIDs support interoperability, working across different platforms and services. This flexibility ensures users maintain control over their identity across various applications, enhancing privacy and security. By utilizing SSI and DIDs, trust can be established in a decentralized network efficiently and securely.
Regulatory Compliance
Cryptocurrency regulations require stringent measures to prevent illegal activities. Two critical aspects are Anti-Money Laundering (AML) initiatives and Know Your Customer (KYC) policies.
Anti-Money Laundering (AML) Initiatives
AML initiatives are designed to detect and prevent money laundering activities that can be facilitated through blockchain transactions. Financial institutions must implement strict monitoring systems. These systems track and analyze transactions for suspicious activity patterns.
Blockchain technology provides transparency, which helps in identifying and stopping illegal financial activities. Authorities often require detailed reports of large transactions and the identification of involved parties. This helps trace the source and destination of funds, reducing the risk of dubious operations.
Know Your Customer (KYC) Policies
KYC policies require financial institutions to verify the identities of their clients. This is crucial in preventing fraud, identity theft, and other illicit activities. Clients must provide valid identification documents, such as passports or driver’s licenses.
Blockchain transactions typically include data encryption, which is essential for securing personal information. KYC compliance ensures that only legitimate users can engage in blockchain transactions, thus maintaining a secure and trustworthy environment. By implementing KYC processes, organizations can mitigate risks and ensure regulatory adherence.
]]>Privacy and Security: The Dual Pillars of zk-Proofs
Cryptographic techniques such as zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Argument of Knowledge) are crucial in implementing these proofs efficiently. zk-SNARKs provide a compact proof that can be verified quickly, making them suitable for modern blockchain networks. Their integration into blockchain systems facilitates seamless and secure transactions without compromising user privacy.
Privacy technology in this context extends beyond simple encryption. It encompasses advanced methods to maintain data integrity and confidentiality while ensuring trusted interactions. As digital transactions become more pervasive, the demand for robust privacy solutions like zk-Proofs continues to grow, reshaping the landscape of secure online communications.
Key points
Definition and Basic Principles
Zero-knowledge proofs (zk-Proofs) are cryptographic protocols that allow one party to prove the truth of a statement to another party without revealing any additional information beyond the validity of the statement itself.
- Specific Type: zk-SNARKszk-SNARKs (Zero-Knowledge Succinct Non-Interactive Argument of Knowledge) are a specific type of zk-Proof that are especially valuable in blockchain due to their efficiency and the fact that they do not require interaction between the prover and verifier.
- Blockchain ApplicationsPrivacy in Transactions: zk-Proofs ensure that transaction details like the amount and parties involved remain private while still being verifiable.
- Data Verification: Enables the verification of data integrity and authenticity without exposing the underlying data.Decentralized Identity: Users can prove identity attributes without revealing personal information.
- Other Privacy Technologies in BlockchainRing Signatures and Confidential Transactions are additional methods used alongside zk-Proofs to enhance privacy by obscuring transaction details and sender identity.
Challenges and Limitations
- Scalability: Incorporating privacy features can reduce transaction speed and increase computational demands.
- Regulatory Challenges: Privacy features must be balanced with regulatory requirements for transparency.
- Usability: Advanced privacy technologies often require significant technical knowledge, which can be a barrier for average users.
Overview of Zero-Knowledge Proofs
Zero-knowledge proofs (zk-proofs) are cryptographic methods used to prove that a statement is true without revealing any specific information about that statement. They enable one party (the prover) to demonstrate to another party (the verifier) that they know a value without disclosing what that value is.
A common use case in blockchain technology is privacy. zk-proofs help ensure that sensitive information remains confidential while still allowing transactions to be verified. For instance, zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Arguments of Knowledge) is a particular form of zero-knowledge proof.
Key Features
- Privacy: No information about the secret is revealed.Soundness: The verifier can be confident that the prover knows the secret.
- Efficiency: Proofs are quick to verify and require minimal resources.
Applications
- Cryptocurrency transactions: Enhancing privacy in financial transactions.Authentication: Proving identity without sharing personal credentials.
- Data verification: Confirming data integrity without exposing the data itself.
Zero-knowledge proofs are transforming the way privacy and security are managed in various fields, making them a fundamental component of modern cryptographic techniques.
Cryptography in Blockchain
Cryptography in blockchain technologies ensures both the security and privacy of data and transactions. It plays a critical role in maintaining trust and integrity in decentralized systems.
Role of Cryptography
- Cryptography is essential for securing the data within a blockchain. It involves encryption and hashing to protect transaction information. Encryption converts data into coded formats that can only be accessed with a decryption key, ensuring unauthorized parties cannot read it.
- Public-key cryptography allows users to generate a public and private key pair. The public key is shared publicly, while the private key remains confidential, enabling secure transactions without intermediaries.
- Hash functions create a unique digital fingerprint of data, ensuring data integrity. Any alteration in the input produces a significantly different output, produces a significantly different output, making tampering evident.
Blockchain Security Mechanisms
Blockchain employs cryptographic techniques to ensure the integrity and security of its infrastructure. One key mechanism is the Proof of Work (PoW), used in networks like Bitcoin. Miners solve complex cryptographic puzzles, validating transactions and adding blocks to the chain.
- Proof of Stake (PoS) is another mechanism, where validators are chosen based on the number of coins they hold and are willing to ‘stake’ as collateral. This reduces the computational power needed, providing an energy-efficient alternative.
- Cryptographic signatures also play a vital role. Digital signatures guarantee that messages or documents are authentic and have not been altered. Users sign transactions with their private keys, and the network uses the public key to verify the signature.
Zero-Knowledge Proofs in Blockchain
Zero-knowledge proofs (zk-proofs) enhance blockchain by enabling secure and private transactions without revealing underlying data. This section explores trustless verification and practical applications within the blockchain ecosystem.
Trustless Verification
Zero-knowledge proofs support trustless verification by allowing one party to prove to another that a statement is true without disclosing any information beyond the truth of the statement itself.
In blockchain, this is particularly valuable for ensuring transaction validity without compromising user privacy. Validators can confirm the authenticity of data while the actual data itself remains hidden. This reduces the need for intermediaries and mitigates risks associated with data breaches. Zk-proofs help maintain the decentralized and transparent nature of blockchain while enhancing security.
zk-Proofs Applications
Applying zero-knowledge proofs in blockchain can address several use cases. One notable application is in confidential transactions, where transaction details, such as amount and parties involved, are kept private yet remain verifiable on the blockchain. Decentralized identity management also benefits, enabling users to prove their identity attributes without exposing their actual identity data.
Another application is scalable voting systems, which ensure that votes are counted correctly without revealing individual voter choices. Additionally, zk-proofs enhance smart contract privacy, allowing execution of contract conditions without public exposure of sensitive information. This broadens the potential use cases for blockchain technology across various industries, from finance to governance.
Privacy Technology in Blockchain
Blockchain technology integrates various privacy techniques to secure data and maintain confidentiality. One significant method involves zero-knowledge proofs, which allow information to be verified without revealing the data itself.
Enhancing PrivacyBlockchain uses zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Arguments of Knowledge) to enhance privacy. This cryptographic method allows one party to prove possession of certain information without revealing that data. Through zk-SNARKs, transactions can be validated without exposing sensitive details, thereby enhancing user privacy. Another technique is ring signatures. Ring signatures enable secure and anonymous transactions by grouping a sender with others, making it unclear who initiated the transaction. This method ensures privacy while maintaining the integrity of the blockchain. Confidential transactions represent another approach. By encrypting transaction amounts, only the involved parties can see the details. This method significantly improves financial privacy on the blockchain.
Challenges and Limitations
Despite its advantages, privacy technology in blockchain faces several challenges. Scalability remains a significant issue, as implementing privacy features can slow down transaction processing times and increase computational complexity. Regulatory concerns also pose a challenge. Governments and regulatory bodies often require transparency for anti-money laundering (AML) and know your customer (KYC) purposes, which can conflict with privacy measures.
Moreover, usability can be a hurdle. Integrating privacy technologies such as zk-SNARKs can be complex and require advanced technical expertise, making it harder for the average user to adopt these solutions. Legislation, scalability, and usability continue to impact the widespread adoption of privacy technologies in blockchain, requiring ongoing innovation and development.
]]>
zk-Proofs: Enhancing Privacy and Security in Blockchain
Zero-knowledge proofs are revolutionizing the field of cryptography by enabling one party to prove they have knowledge of specific information without revealing the information itself. This breakthrough has profound implications for privacy in blockchain technology. By maintaining the confidentiality of transaction details, zero-knowledge proofs enhance both security and privacy.
zk-SNARKs, a specific type of zero-knowledge proof, are gaining traction within blockchain applications. They enable efficient verification of transactions while keeping the underlying data private. These proofs allow blockchain networks to scale more effectively, as they reduce the amount of data that nodes need to process.
Privacy technology within blockchain is critical for ensuring user trust and protecting sensitive information. As digital transactions become increasingly common, robust privacy measures like zk-SNARKs are essential for maintaining the integrity and security of blockchain ecosystems.
Key Points
- Zero-Knowledge Proofs in Cryptography: The concept that zero-knowledge proofs allow a party to demonstrate knowledge of certain information without revealing the information itself is a fundamental aspect of these cryptographic techniques. This enhances privacy and security in digital interactions.
- zk-SNARKs: Accurately describing zk-SNARKs (Zero-Knowledge Succinct Non-interactive Arguments of Knowledge) as a type of zero-knowledge proof that is particularly useful in blockchain applications. Their ability to provide efficient verification of transactions while maintaining privacy of the underlying data is correctly emphasized.
- Applications and Benefits: The mention of zk-SNARKs in cryptocurrency, such as their use in Zcash for privacy-preserving transactions, and their potential in secure voting and authentication protocols highlights the practical applications of this technology.
- Blockchain Integration: Describing correctly points out how zk-Proofs integrate with blockchain technology to enhance privacy, scalability, and security. They allow for the verification of transactions without revealing sensitive information, which is particularly beneficial in public blockchain environments where privacy concerns are paramount.
- Challenges and Future Directions: The discussion about the challenges in implementing zk-Proofs, such as the complexity of cryptographic methods and performance issues, as well as the ongoing research into making these proofs more efficient and interoperable across different platforms, provides a balanced view of the current state and future potential of this technology.
Fundamentals of Cryptography
Cryptography forms the backbone of secure communication and data protection in digital systems. It involves various techniques and principles designed to protect sensitive information from unauthorized access.
At its core, cryptography employs encryption and decryption processes to protect data.Encryption converts plaintext into ciphertext, making it unreadable to anyone who doesn’t possess the correct key. Conversely, decryption turns the ciphertext back into readable plaintext.
Zero-Knowledge ProofsZero-knowledge proofs (zk-proofs) allow one party to prove to another that they know a value or solution without revealing the value itself. This technology is essential in cryptography and has diverse applications in ensuring privacy and security.
Principles of Zero-Knowledge Proofs
Zero-knowledge proofs adhere to three main principles: completeness, soundness, and zero-knowledge. Completeness ensures that a correct statement can be proven true. Soundness guarantees that a false claim cannot be proven true. Zero-knowledge implies that no information besides the validity of the statement is revealed. These principles underpin the effectiveness of zk-proofs, making them invaluable in secure communications and data verification without exposing sensitive information.
Types of Zero-Knowledge Proofs
Zero-knowledge proofs are generally divided into interactive and non-interactive types. Interactive zk-proofs require communication between the prover and verifier multiple times to establish proof. Non-interactive zk-proofs (NIZK) achieve the same in a single exchange, enhancing efficiency.
Other notable categories include zk-SNARKs (Succinct Non-interactive Arguments of Knowledge) and zk-STARKs (Scalable Transparent Arguments of Knowledge). zk-SNARKs offer brevity and expediency, while zk-STARKs prioritize scalability and transparency.
Applications of Zero-Knowledge Proofs
Zero-knowledge proofs are crucial in various fields, including cryptocurrencies, secure voting systems, and authentication protocols. For cryptocurrency, zk-proofs enable privacy-preserving transactions, as seen in Zcash with zk-SNARKs.In secure voting, zk-proofs can verify voters’ eligibility without disclosing their identities. For authentication, zk-proofs provide secure and private logins, reducing the risk of data breaches. These applications highlight zk-proofs’ potential in enhancing privacy, security, and efficiency in digital interactions.
zk-Proofs in Blockchain Technology
Zero-knowledge proofs (zk-Proofs) have emerged as a significant advancement in blockchain technology, enhancing both security and privacy. This section will examine the fundamentals of blockchain and explore the specific role that zk-Proofs play within this technology.
Blockchain Basics
Blockchain is a decentralized ledger technology that records transactions across numerous computers. This decentralized nature ensures that the data is immutable and transparent. Each block in the chain contains multiple transaction records, and once a block is added, it cannot be altered, ensuring data integrity.In blockchain, consensus algorithms such as Proof of Work (PoW) or Proof of Stake (PoS) are used to validate transactions. These methodologies allow participants to agree on the current state of the blockchain. Decentralization, transparency, and immutability are the core principles that define blockchain technology.
Importantly, blockchains can be either public or private. Public blockchains are open to everyone, while private blockchains restrict access to certain users. Both types benefit from zk-Proofs, but the advantages are often more pronounced in public blockchains where privacy and security concerns are paramount.Role of zk-Proofs in Blockchainszk-Proofs enable the verification of data without revealing the data itself. This feature is crucial for maintaining privacy while ensuring the integrity of transactions. In blockchain, zk-Proofs are particularly useful for tasks such as transaction validation without exposing sensitive information.
For instance, zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Arguments of Knowledge) are a type of zk-Proof used extensively in blockchain applications like Zcash. They allow users to prove ownership of a secret (e.g., a private key) without revealing the secret itself. This verification process is done quickly and efficiently, with minimal computational overhead.
In addition to privacy, zk-Proofs contribute to scalability. By enabling privacy-preserving proofs with low computational requirements, they can help blockchains process a larger number of transactions more efficiently. This makes zk-Proofs an essential tool for enhancing both privacy and performance in blockchain networks.
zk-SNARKs
zk-SNARKs, or Zero-Knowledge Succinct Non-Interactive Arguments of Knowledge, are a powerful cryptographic tool used in blockchain technology. They enhance privacy and efficiency by allowing one party to prove possession of certain information without revealing the information itself.Understanding zk-SNARKszk-SNARKs enable proofs to be both succinct and non-interactive. A proof can be verified quickly compared to traditional proofs, and no back-and-forth communication is required between the prover and verifier. These properties make zk-SNARKs suitable for scalable and efficient verification in blockchain systems.
Constructing zk-SNARKs
Constructing zk-SNARKs involves complex mathematical concepts, including elliptic curves and quadratic arithmetic programs (QAPs). Provers use these elements to convert a computation into a form that can be succinctly and verifiably proven. Moreover, a trusted setup phase is often required to generate keys that are used in the construction of zk-SNARKs.
Utilizing zk-SNARKs in PracticeIn practice, zk-SNARKs are integrated into various blockchain projects to enhance privacy. For instance, Zcash utilizes zk-SNARKs to enable shielded transactions, which mask both the transaction details and the involved parties’ identities. This way, zk-SNARKs significantly improve the confidentiality of blockchain transactions without compromising the security of the network.
Privacy Enhancements and Challenges
zk-Proofs provide significant advancements in privacy technology but also face implementation difficulties. These complexities can affect the deployment and usability of zero-knowledge proofs.
Advances in Privacy Technology
Recent innovations have made zero-knowledge proofs (zk-Proofs) more practical for blockchain applications. Among these innovations, zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Arguments of Knowledge) stand out due to their efficiency in verifying transactions without revealing any private information.
- Merits include: Scalability: zk-SNARKs require minimal computational resources.
- Privacy: Users can validate transactions without disclosing personal data.
- Efficiency: The succinctness of zk-SNARKs reduces storage and bandwidth requirements.These advancements are being integrated into various blockchain platforms, enhancing both privacy and performance.
Challenges in Implementing zk-Proofs
While zk-Proofs offer numerous benefits, their implementation comes with challenges. Configuring zk-SNARKs requires specialized cryptographic knowledge, which can be scarce.
- Challenges include:Complexity: The cryptographic methods behind zk-SNARKs are intricate.
- Performance: Despite improvements, zk-SNARKs can still be resource-intensive.
- Interoperability: Making zk-Proofs work across different blockchain platforms can be problematic.
These challenges require ongoing research and development to ensure wider adoption and smoother integration of zero-knowledge proofs in blockchain technology.
Future Landscape of zk-Proofs
The future landscape of zero-knowledge proofs includes advancements in efficiency and new applications in privacy-preserving technologies and blockchain enhancements.
Innovations in zk-Proofs
Researchers are focusing on improving the efficiency of zero-knowledge proofs. Key areas include reducing both proof size and verification time. Smaller proofs mean less computational burden and faster transactions, crucial for scalability. Recursive zk-Proofs are another promising development, allowing multiple proofs to be nested and verified simultaneously. This approach can greatly optimize complex operations in blockchain systems and other cryptographic applications.Post-quantum security is also critical. Developing zk-Proofs resistant to quantum attacks is becoming increasingly important, ensuring long-term security as quantum computing technology advances.
The Road Ahead for Privacy and Cryptography
Zero-knowledge proofs will play a significant role in enhancing privacy within blockchain applications. By enabling parties to prove assertions without revealing underlying data, they offer robust privacy solutions for sensitive transactions.Interoperability will be another key focus. zk-Proofs could facilitate seamless interaction between different blockchain networks, enabling more comprehensive and versatile applications. Regulatory compliance is another important area. zk-Proofs can help meet privacy regulations like GDPR while still ensuring data integrity and transparency. This balance between privacy and compliance will be crucial as technology continues to evolve.The integration of zk-Proofs into mainstream cryptographic practices will drive innovation, providing new levels of security and privacy in various digital realms.
]]>Since 2020, DAOs have become more well-known and have gradually become mainstream players in the blockchain industry. Recently, we have seen major venture capital institutions disclosing their investments in DAO projects, which has attracted the attention of major blockchain media. Therefore, some people think that “2022 will be the first year of DAO.”
What is it about DAOs that attracts the interest of these market-leading investment institutions and the associated media??
Understanding DAOs
Human beings have entered the DAO era, and all this cannot be avoided.
— Stephenson, the Father of the Metaverse
Everyone has their interpretation of what a DAO is, but they all share a common logic: members vote with tokens, and open-source codes automatically run voting results. This trustless system eliminates human error and members can manage community finances as a collective. 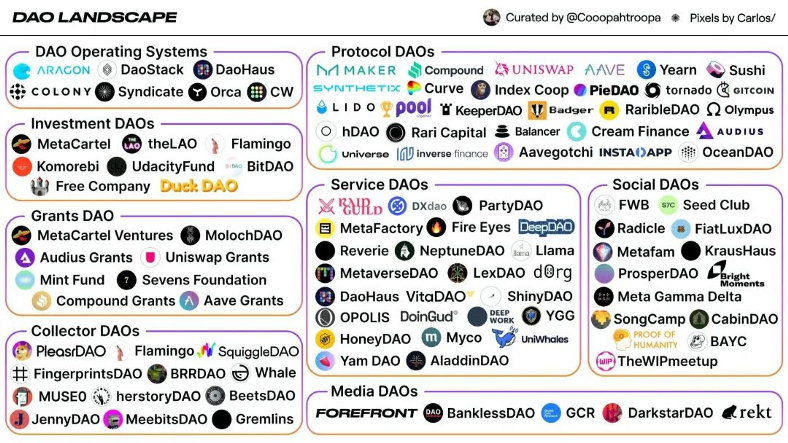
Source: The DAO landscape.
At present, DAOs have developed across many platforms, including social media, agreement platforms, project principles, and so on. Moreover, it is more like a bottom-up management company, where members rely on their personal abilities and subjective wishes to divide labor to build the entire DAO. The DAO will reward members based on their contribution value.
In the upcoming Metaverse, DAOs may well be at the core of governance models, as it returns the rulemaking and governance power to the public, promoting the complete decentralization of the Metaverse.
Still In Early Stages
Whilst the vision for DAOs is beautiful, the reality is still working towards fulfilling these goals. It is true that people in the decentralized field are increasingly interested in DAOs, but the development of DAOs still faces difficulties. These hurdles include:
Low Member participation
Most DAOs use the digital assets of their members as key indicators. For example, voting is based on the number of tokens, and rewards are based on the proportion of digital assets. This approach not only inhibits the voice of DAO members but also makes members with a small proportion of tokens unwilling to invest time and energy in governance, due to the imbalance of investment returns.
Centralization crisis
The above-mentioned system employed by DAOs can easily lead to the emergence of a mindset that “the rich will always be rich, and the strong will always be strong”. The simple reality is that with the right to speak, comes the right to set rules that are more beneficial to you, and you can get greater benefits. This has pushed many DAOs into an unwanted centralized situation.
Decisions are difficult to balance
In a fully autonomous DAO system, the decision should be based on the number of votes. But sometimes there are conflicts between the opinions of the development team and the interests of community members. How to maintain a good balance is a headache for many DAO organizations. Sometimes the DAO development team will directly ignore the community opinions, resulting in accusations of centralization. The alternative is to completely follow the DAO community, which may result in constructive opinions not being adopted.
Which Brings Us to Reputation
The above problems essentially have a key point: what kind of incentives should be set up? The incentives should not only satisfy decentralization and fairness but also promote proactive DAO members that actively participate in governance. 
Based on its own technology and past service experience, Ontology proposes the following solution: Set up a DID with a reputation scoring system for each DAO member.
Verification
When you enter a DAO, you need to first register/own a DID and submit certain verifications (authorization through encryption to protect privacy), such as on-chain/off-chain assets, whether you have similar experience or capabilities, and so on. After verification, you will be given an initial value and mark to help you better participate in DAO.
Record
When participating in DAO governance, DID will record the amount time spent in the DAO and your contributions after joining. Contributions would include voting, suggestions, operational work, and so on. If you also use this DID to participate in the governance of other DAOs, those data will also be recorded in the same DID, increasing your data diversity.
Reputation Score
The reputation system will make a comprehensive score based on the above records. For example, the more DAOs you participate in, and the longer, and the more active you are, the higher your score will be. In addition, corresponding weights can be set when designing the reputation scoring model, such as reducing the weight of digital assets and increasing the weight of participation.
Decentralization
With reputation value, DAO can dynamically divide rights based on reputation. The higher the reputation value, the greater the power. This power could be manifested in the right to more votes (right to speak) and the right to more DAO dividends.
Participation
Based on this, we can imagine a completely decentralized DAO organization as:
- The acquisition of rights and benefits is no longer difficult for ordinary members.
- The development team, like ordinary members, needs to rely on contribution to gain the right to speak.
- It has become very important to increase your participation and enthusiasm.
To Summarize
Implanting DID in DAOs can eliminate “centralization” based on digital assets to a certain extent. DID can encourage DAO members to become more active, and balanced decision-making between the development team and ordinary members.
Whilst DID can help to solve some of the current DAO problems, this is still only the beginning.
In the future, DAOs will inevitably become the organizational form of the decentralized world, with more blockchain technologies being absorbed by DAOs, allowing for the quick and healthy development of ecosystems.
]]>As the world moves towards the next iteration of the internet, we continue with our efforts to build the infrastructure required for a new generation of decentralized applications. Ontology aims to deliver a seamless experience for both developers and the users who interact with their projects. To do so we are looking for talented people, with the vision to match their abilities.
We are thrilled to have compiled a thorough list of all the positions we are looking to fill with awesome new team members! Whether you are looking for technical positions in development, or positions in marketing, business development, human resources… chances are, we have an opening for you.

If you or anyone you know is a perfect fit for any of the roles above, please feel free to contact us at careers@ont.io for more details. Our global Harbingers are also glad to help you onboard. Looking forward to meeting you and having you join us in our mission to bring true decentralization to identity & data practices!
]]> Introduction
Introduction
2021 draws to a close with Web3 firmly establishing itself in the consciousness of the crypto community. Perhaps more importantly, we have started to see signs that it is transcending into the minds of those outside of the cryptosphere. Web3, in its association with the Metaverse, looks set to capture the imaginations of people worldwide in 2022.
Ontology has worked on bringing trust, privacy, and security to Web3 through providing decentralized identity (DID) and data solutions. From the very inception of the project, the aim has been to build the infrastructure required for users to interact with this new generation of decentralized applications, and that aim has not changed.
Our goal for 2022 is to make the Ontology high-speed, low-cost, public blockchain, the blockchain of choice for Web3 applications. Ontology’s efforts in creating interoperability between the different public chains, including the upcoming Ontology Ethereum Virtual Machine (EVM) launch, will provide the opportunity to incubate more high-quality Web3 applications in the new year across a multitude of industries and services.
Beyond providing a blockchain to build Web3 applications, delivering ease of access and a seamless experience is essential to the user experience. That is why ONTO Wallet aims to become the access point of choice in 2022, providing the easiest access to Web3 for every user by allowing them to own their identity and data. This approach of empowering developers and users alike, to build and experience together, underlines Ontology’s goals for 2022.
Decentralized Identity and Data
Web3 should allow you to have self-sovereign identity and data, and it should allow you to choose which parts of your online existence, or perhaps we should say your existence in the Metaverse, you’d like to share with each other. This requires technical interconnectivity and interoperability, as well as more philosophical and collaborative discussions across the entire community for how identity is defined and changed.
In the end, there will not be a single blockchain, but rather a collection of different chains, each with their own characteristics, benefits, and subcultures. Whilst there will be competition, there is also tremendous opportunity for collaboration for the benefit of the overall ecosystem and user experience.
Ontology will continue to optimize deeper product integrations across different blockchains. With a focus on DID and data, users will be on-boarded into the Ontology experience for secure, self-sovereign control over their digital existence.
The launch of the new ONT.ID website brings us 1 step closer. ONT ID, ONT Login, and ONT TAG empower both developers and users by providing cost-effective and private methods to authenticate and manage their identities.
Multi-VM
Virtual Machines (VMs) play a crucial role in both the aforementioned need for interoperability and in the expansion of applications built on Ontology. By taking a Multi-VM approach, Ontology maximizes interoperability and allows more developers to create in the development languages they are familiar with. The Ontology EVM will be launched in Q1 2022, together with an EVM Fund to incubate the development of applications on Ontology.
The launch is the culmination of all the hard work by the team that began at the start of 2021 when Ontology’s tech team first began developing the Ontology EVM. The EVM, along with the EVM fund, aims to establish seamless interoperability between Ontology and the Ethereum platform and to offer an inclusive experience to developers and users. The new VM will join a suite of existing VMs, which include the Native (Ontology) VM, NeoVM, and WasmVM.
This is a crucial step in the realization of the Ontology Multi-VM. It adds to the opportunities provided by the WasmVM, which allows more traditional developers to deploy apps on the blockchain. As the most common virtual machine used on the traditional Internet, the support of Wasm also prepared Ontology for big-scale Web2 applications to transition to Web3 in the near future.
From a dApp development perspective, the Multi-VM approach taken by Ontology allows dApps to be integrated into multiple platforms. This boosts long-term growth for cross-chain dApps, exposing them to a larger user base and to receive all the benefits offered by the various alternative chains.
Web3
This Multi-VM approach, combined with a focus on DID and data, brings us back to the importance of Web3. Since the very beginning, Ontology has been building the infrastructure necessary for a cross-chain, interoperable Web3.
Ontology will continue to vigorously develop the following products, already familiar to the community:
ONT ID will be optimized to be more applicable to all blockchains, including products like ONT TAG, ONT Login, and OScore. Over 1.5 million users now manage their digital identity using ONT ID, with control over how, when, and with whom their data is shared. Furthermore, we continue to work on the design of more DID products for developers to further expand DID applications.
ONTO Wallet, as the essential gateway for every individual to Web3, aims to provide crucial infrastructure for a seamless Web3 experience. Over the past year, we have seen tremendous growth in ONTO users (over 750K), and its social influence, with 30 times increase in social media channels and communities.
With ONTO, users can create their decentralized identities and verify credentials, powered by Ontology’s decentralized identity framework. The ONT ID digital identity wallet allows users to use a single private key to log into their multi-chain wallets. They can also manage their digital assets, including NFTs, perform cross-chain swaps, keep up-to-date with the latest industry developments and events via the ONTO news feed, and enjoy access to a full range of dApps anywhere and anytime, available as both mobile and web applications. Moving forward, ONTO will continue to expand its multiple chains assets and dApps support, making Web3 easily accessible in the palm of your hand.
The decentralized digital asset and distribution tool, ONTO Anydrop, also provides faster, cheaper, and more convenient event support for our partners, and will continue to benefit the expansion of our ecosystem.
Wing Finance will continue to utilize Ontology’s decentralized reputation solution for DeFi projects. Its unique and pioneering Inclusive Pool, coupled with Ontology’s OScore, allows people to under-collateralize assets and maximize their borrowing capabilities based on Web3-native credit and reputation scores.
Ontology will continue to work with Wing to develop further product lines, which will enable more types of assets to be lent, borrowed, and collateralized. There will also be continued expansion of accessibility, allowing more users to enter the DeFi ecosystem.
SAGA provides data management in the Web3 era. Offering a decentralized alternative, where the data providers remain in control of their data.
Thanks to these platforms and more, whether it is DeFi, GameFi, NFTs, or one of the countless other innovative decentralized applications, Ontology is well placed to support their development and expansion. Ontology will keep developing more easy-to-use products and tools to meet the requirements of the era, making Web3 available to everyone, whilst maintaining the security and privacy of users, and bringing a decentralized experience to the world.
Looking Ahead
2021 draws to a close and 2022 promises to bring us closer to Web3 than ever before. Four years of work has positioned Ontology as a leader in the space, through the development of products focused on DID and data, and by taking a Multi-VM approach.
The upcoming launch of the Ontology EVM and the associated EVM fund will bring the benefits of Ontology to a new, larger audience. More applications will be built on the Ontology network, expanding the opportunities for developers and users alike. The relevance and application of the Ontology approach extend to the entirety of Web3, regardless of the chain.
No doubt 2022 will bring new tech advancements, alongside ecosystem growth. We’re excited to journey into the decentralized future with you and appreciate all the support shown by our community throughout the year. Our Harbingers have continued to work passionately, to provide the best community experience possible. We are always looking to recruit more Harbingers into the Ontology family, and hope to welcome more new faces in the new year.
Ontology is proud to be part of this rapidly changing landscape and is excited to share more updates in the future. Here’s to another year exploring the future together.
]]>In order to acknowledge and reward those who participate in Ontology’s events and contribute to our weekly discussions, we are launching a loyalty program! Engage with the community and receive NFTs. Collect enough NFTs to win ONG rewards!
Ontology’s Loyal Member program aims to boost the community’s knowledge about Web3 and blockchain, as well as decentralized identity solutions. It is also a way for us to give back to community members who contribute to our events and grow with the Ontology family. Ontology is going to give away NFTs to specific community members whose contributions stand out. Members who collect 10 Loyal Member NFTs can receive 50 ONG.
The Loyal Member program gives Ontology community members the opportunity to learn more about our ecosystem and each other. We hope to facilitate more connections with our community members and encourage a welcoming atmosphere for new members interested in blockchain technology.
How to Attend
Join our Telegram group and share your topic with the hashtag #Topic directly in the group channel.
At the end of our weekly Tuesday Community Call, we will have an anonymous vote for your favorite topic for Wednesday. The most popular topics will be discussed at 9am UTC on Wednesdays.
Some potential topics include DID, Web3 and NFTs. Bring your own idea to the table and share it with the community.
Our study panel will be held on a weekly basis. Those who are active and participate will be noted by admins and will receive a special NFT acknowledging their contributions.
The first 10 members to receive 10 NFTs will be awarded 50 ONG each.
How to Claim
We will collect active members’ Ontology addresses to airdrop the NFTs. Once the NFTs reach 10, we’ll distribute 50 ONG to the related address. Each member/address can only receive ONG once.
Note: The Ontology Team reserves the final right of interpretation of the above event.
]]>